Search Carrier Jobs

We Break New Ground by Working Together
At Carrier, we make modern life possible by delivering groundbreaking systems and services that help homes, buildings and shipping become safer, smarter and more sustainable. We exceed the expectations of our customers by anticipating industry trends, and working tirelessly to master and revolutionize them.
Our global team of dedicated employees continues to set industry standards by pursuing the latest research and developments to improve the lives of our customers. We’re constantly growing and seeking out talented, likeminded people who are committed to our primary duty: to be the world’s first choice in shipping and HVAC technology.
Career Areas

Incorporating areas such as Finance, Marketing, General Management, Human Resources, Communications & Legal, Carrier's Corporate functions support the smooth Global operation & delivery of world class services across the Carrier Organization.

The Digital Technology team is comprised of functional areas such as Computer Engineering, Cybersecurity, infrastructure and technology functions. The Foundry also sits inside of our digital function which is the main project owner for our world class services such as Abound and Lynx.

Be supported, as you kickstart your career, by industry leading teams with the global leader in the sector. It is not an easy job, but one you can shape and make your own. Your future is in your own hands!
Carrier's Global Leadership Programs & Apprenticeships are a fantastic way for us to turn today’s talented people, like you, into the experts the world needs tomorrow.

Engineering is the lead of our R&D space. With worldwide locations and teams centered in our i3 Innovation hubs, you can find our teams working in areas such as mechanical, electrical, computer science, software and chemical.

The frontline of the Carrier organization, our dynamic sales teams help our customers achieve their goals with our robust portfolio of best-in-class products and services. From developing and nurturing relationships with our partners to providing critical feedback to enhance our solutions, our sales organization is growing to take Carrier to the next level.

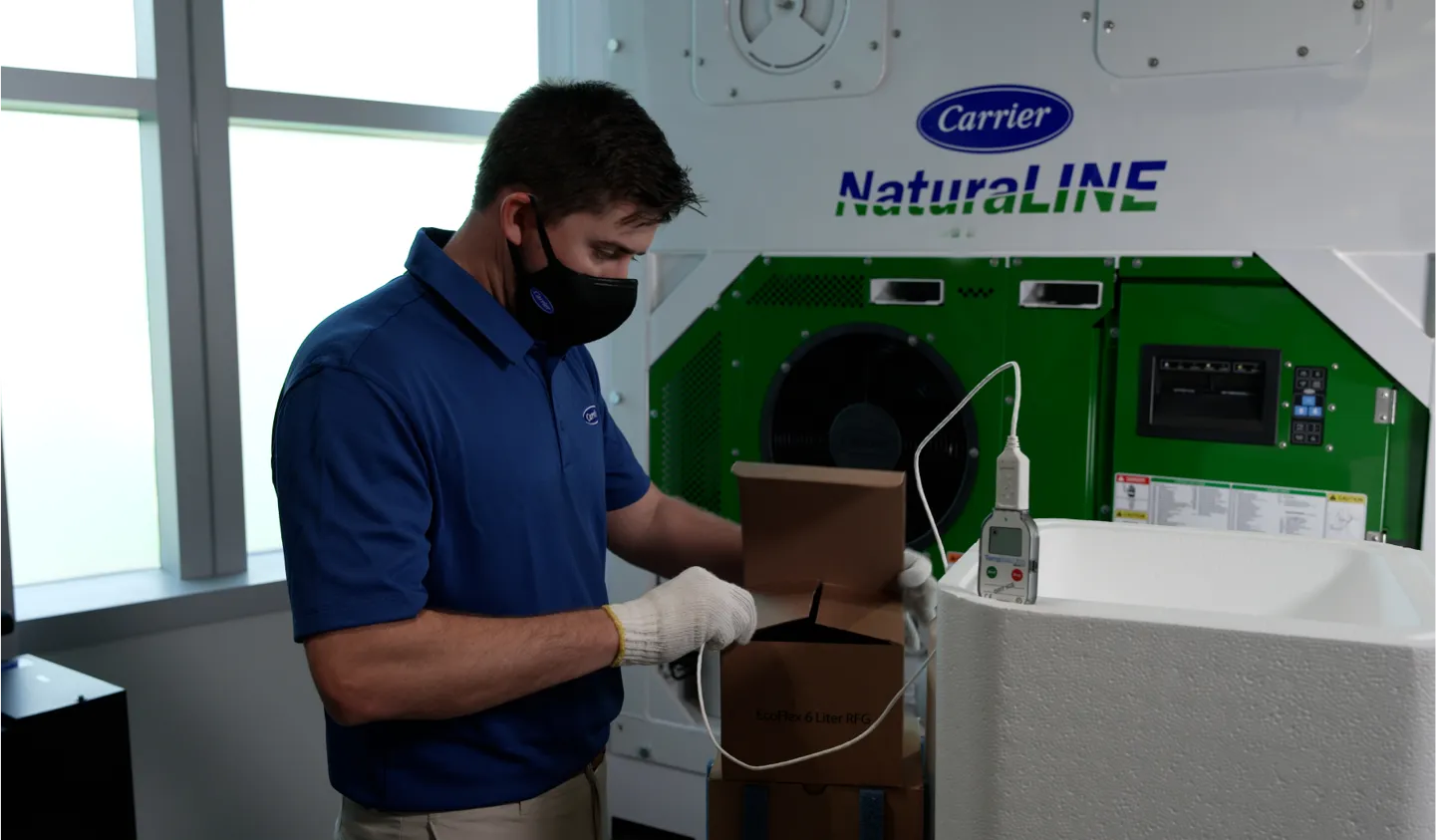
Our Service Technician teams ensure the highest quality customer service by understanding the intricacies of our customer’s business and daily needs.
With a wide range of innovative solutions: operations and maintenance, service agreements, modernization solutions, controls, parts and rental, our team is able to deliver the best in class service during the equipment lifecycle.
Operations is the heart of what we do. Our global locations support production, supply chain, EH&S, and our Carrier Excellence goals. Our world class products are built, inspected and shipped from our facilities by our diverse and talented teams.

Explore Careers in Carrier Business Services

Inclusion & Diversity
Our greatest strength is the diversity of our people and their ideas. We are committed to a workplace that is truly and genuinely inclusive, one that inspires and encourages everyone, everywhere, to bring their authentic selves to work, every single day. Carrier remains steadfast in our goal to create a workplace that is truly and genuinely inclusive, and where all employees feel like they _belong.
Hear From Our Team
I like to work together in cross-regional teams with all hierarchy levels. This enables us to bundle all skills, learn from and challenge each other.
Montluel, Frankrijk

At Carrier, we truly value our employees and culture, and that enables us as employees to grow and feel passionate about our careers.
Europe, France

I'm constantly learning new things at Carrier. The company offers a variety of training programs and development opportunities, and I'm always encouraged to take on new challenges. I'm grateful for the opportunities to grow my skills and advance my career.
India

I'm proud to work for a company that is committed to inclusion and diversity. Carrier has a diverse workforce, and we are all treated with respect and dignity. I feel like I can be myself at work, and I'm able to bring my unique perspective to the table. I also enjoy the way we collaborate with different teams globally and work together on varied challenges.
India

The Carrier Engineering Leadership Program (ELP) was an invaluable experience that I wouldn’t trade. In each rotation, my development was promoted not only by the meaningful projects that I was challenged to take on, but by the people who invested in my growth. The program allowed me to explore diverse career opportunities, practice leadership skills, grow in technical competencies, and build a network of experts throughout Carrier who all share a common goal - creating solutions that matter for people and our planet!

The best part about working at Carrier is working with a diverse team of people from different walks of life, people from different countries, people with different abilities, and that's what makes it a great place to work.
Palm Beach Gardens, FL

Everyone's opinion is heard and that's how we bring productivity into the environment.

